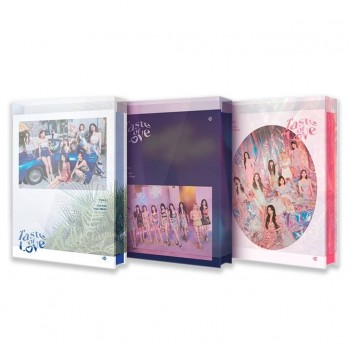
YG OFFICIAL
MERCHANDISE
on sale!

Online Support
Trained staffs are ready to help

Money Back Guarantee
100% money back guarantee

Free Shipping
Free shipping on all orders over ₱3000


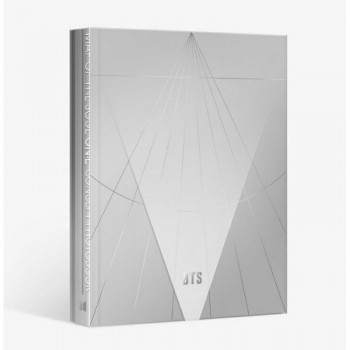
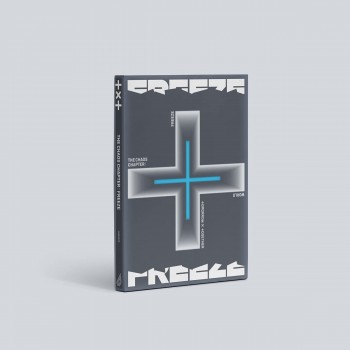
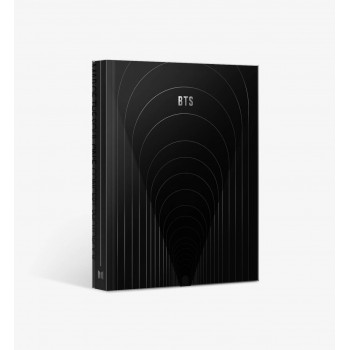
OFFICIAL BTS
MERCHANDISE
now available!
Save up to 30% on selected items!
Shop Now
Featured
Collection


![BLACKPINK 2021 [THE SHOW]...](https://merchdive.com/37-home_default/blackpink-2021-the-show-live-cd.jpg)